How Technology Will Shape Crypto
Technology will continue to weave interoperable protocols and modular layers into crypto, enabling cross-network collaboration with disciplined governance. zk-proofs, Layer 2s, and hardware wallets will balance privacy, scalability, and usable security. AI-driven risk tooling and advanced threat detection shorten response cycles, while regulatory tooling supports transparent compliance. The result is resilient yet adaptable ecosystems where innovation is intentional and auditable, inviting further examination of how these forces converge to shape the next phase of crypto infrastructure.
What Tech Forces Are Redefining Crypto Today
Tech innovations are reshaping crypto by altering how trust is established, assets are transferred, and networks scale. The landscape advances through interoperable protocols, open governance, and composable layers that empower participants.
Yet privacy fatigue and data sovereignty emerge as core tensions, demanding resilient design. Strategic symmetry between permissionless experimentation and accountable stewardship becomes essential for a freedom-centric, sustainable crypto ecosystem.
How Zk-Proofs, L2S, and Wallets Reshape Security and Usability
Where do zk-proofs, Layer 2 solutions, and modern wallets converge to redefine security and usability in crypto? They synchronize cryptographic privacy with scalable throughput, enabling verifiable transactions off-chain while preserving on-chain trust. zk proofs illuminate potential vulnerabilities; l2s reduce friction; wallets integrate seamless control. This convergence promises resilient security, enhanced usability, and freedom through transparent, efficient, user-empowered crypto ecosystems.
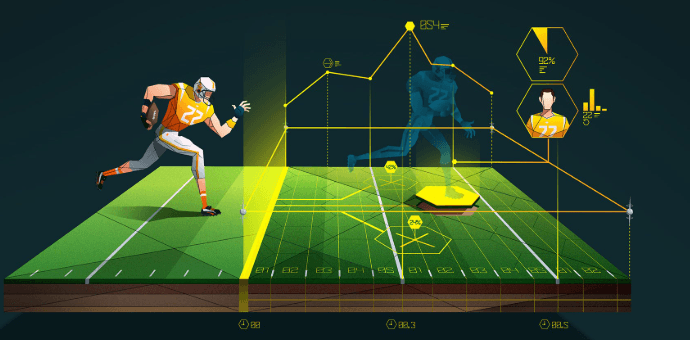
AI, Hardware Advances, and the Changing Security Playbook
AI, hardware advances are redefining the security playbook by accelerating threat detection, shaping response latency, and enabling more resilient cryptographic ecosystems. The shift blends predictive analytics with robust architectures, empowering privacy audits and transparent risk management. Hardware wallets gain traction as trusted anchors, while AI-driven anomaly detection reduces exposure. A disciplined, freedom-loving ethos guides pragmatic adoption, balancing innovation with responsible safeguards and verifiable audits.
Regulation, Compliance, and the Evolving Crypto Regulatory Tech Stack
Regulatory frameworks are evolving in response to rapid crypto innovations, shaping a tech stack that extends beyond code into governance, compliance, and risk management.
This evolving regulatory tech landscape enables proportionate oversight without stifling invention, leveraging compliance tooling to automate controls, monitor flows, and ensure transparency.
Policymakers, technologists, and financiers align to sustain freedom while reducing systemic risk and fostering responsible innovation.
Frequently Asked Questions
How Will Quantum Computing Affect Current Crypto Cryptography Timelines?
Quantum computing hastens the realization of quantum risks, but prudent cryptography timelines emphasize gradual migration. The subject analyzes privacy timelines, balancing risk with innovation while maintaining freedom, resilience, and adaptable standards against emerging computational capabilities.
What Unintended User-Experience Trade-Offs Come With Stronger Privacy Tech?
Privacy tradeoffs include reduced usability friction as stronger privacy tech can complicate onboarding, verification, and recovery; these usability friction points may deter adoption, while long-term freedom hinges on transparent design, informed consent, and interoperable, user-centric privacy abstractions.
Will Central Bank Digital Currencies Coexist With Decentralized Tokens Long-Term?
Central bank digital currencies and decentralized tokens may coexist long-term, as NFT marketplaces and layer 1 governance evolve; the vision remains divergent yet interoperable, with pragmatic safeguards, enabling freedom-seeking participants to leverage complementary value without coercive central control.
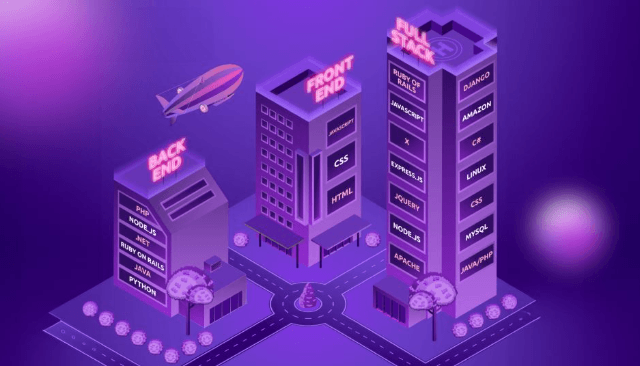
See also: Startup Tech Stack Explained
How Quickly Will Mainstream Wallets Adopt Post-Quantum Standards?
Post-quantum standards will be adopted gradually by mainstream wallets, with crypto adoption accelerating as security stabilizes and developer ecosystems mature, enabling transparent wallet integration that supports rapid, user-centric transitions while preserving liberty and financial autonomy.
Can Ai-Powered Tooling Introduce New Attack Vectors on Exchanges?
A recent 27% spike in AI-driven anomaly detection signals the potential for new attack vectors on exchanges. AI governance and data provenance shape defenses; privacy controls, risk assessment, user education, and security rituals support resilient, freedom-minded systems.
Conclusion
The trajectory outlined signals a crypto landscape where interoperability and modular design unlocks unprecedented collaboration, while open governance and auditable processes ensure accountability. A striking stat: Layer-2 adoption could halve on-chain congestion within five years, boosting throughput and user experience. By blending zk-proofs, hardware wallets, and AI-driven risk tooling, security becomes proactive rather than reactive. Pragmatically, regulatory tech stacks will normalize innovation, not stifle it, enabling resilient ecosystems that scale responsibly and foster inclusive participation.